GOAL
and Tactics |
MONITOR/LEARN
Computer
Monitoring, Sabotage, and/or
Control. |
GATHER DATA
Gathering Electronic Data |
SURVEILLANCE:
Surveillance Cameras, Bugging, Stalking,
and/or Mind
Reading.
Also
Political Surveillance. |
SEND
INFO: Communication and/or Sound Projection |
IRRITATE, REPULSE, CRIPPLE, AND/OR PUNISH:
Includes inflicting
pain, discomfort, or even torture.
(Maybe also sleep
deprivation.) |
MIND
CONTROL
Including Bodymind Control. (Might include
drugging.) |
REMOTE CONTROL OF APPLIANCES
Also see the monitor/learn
category for remote control of computer issues. |
STUN
OR INJURE |
POISON OR KILL: Poison, Radiation, or
Biowarfare |
| How
often this occurs |
Daily. Whenever you're connected to the Internet. |
Infrequently.
Whenever an individual or organization wants to learn about you. |
Some
workplaces and other places have routine electronic surveillance. |
Daily. TV, newspaper, spam. |
Hopefully only very infrequent loud noise disruption. |
Daily. When you're watching TV. |
Variable. Remote control of your own, or sometimes shared, appliances.
(Usually using infra-red technology.) |
Probably never. |
Probably never intentionally.
Rare accidental food poisening. (Est. 5% illness rate/year.) |
| Cheap |
1. Spyware
(can be manually installed on a PC or downloaded from the Internet)
2. Adware (or shareware)
spyware. Often free software
that includes hidden extra programs/ functions.
3. Illegal computer hacking tools
4.keyloggers, rootkits. |
Google,
Investigative Software,
Names, Addresses, & Phone
Numbers Database software.
Street Map software.
Internet
Databases.
Credit Reports.
Driving Records.
Police
Records. |
Computer webcams
and security camera software.
(Infrared webcams/ surveillance
cameras have limited night vision.)
Baby room monitors.
Used spy bugs at eBay.
|
Talk, email, phone
call, fax, letter.
Complain,
protest.
Website
Newsletter
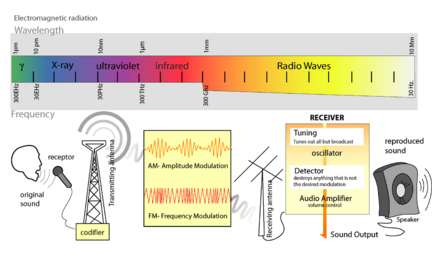
CB Radio
Ham Radio
Walkie
Talkies.
Also self-help subliminal tapes.
Wireless speakers. |
Loud/obnoxious
Music/Behavior, Bad Odors, Graffiti, Vandalism, etc.
(Also note
electromagnetic rodent/insect repellant technology.)
Verbal and/or physical attack by goons. |
Fun: TV (hypnosis
and ads), alcohol
Positive:
positive mind
technology
self-hypnosis
toolsforwellness.com
Negative:
Getting someone drunk with alcohol
Date
rape drugs
dosing with LSD |
V-chip TV content parental control device. Internet filters for
parents and/or employers.
TV-B-Gone. Universal
remote controls.
Remote controlled speakers.
Micro FM transmitters.
Computer spyware/ hacking tools. |
Beststungun.com sells cheap,
weak stun guns. Legal in many areas.
Illegal in
many areas. Restricted in some areas. |
Bad Drinking
Water often carries disease.
Disease: contagious disease routinely travels around the planet.
Spoiled/rotten/moldy food must be avoided.
Poison: Many cleaning liquids are poison (and must be kept away from
infants, for example.) |
| Commercially
Available |
Employee Internet
and/or email monitoring software.
Probably ISP monitoring software too.
(The
FBI claimed in 2003 that they use commercial software.) |
Customer
Databases,
PI (Private Investigator)
Data. |
Videocams, Audio
bugs, phone wiretaps, GPS vehicle tracking.
Spy Tech Agency.
spooktech.com.
Est. 200,000
bugs planted. |
TV
Radio
Newspaper
Magazine
Advertising
Subliminal
ad messages.
Sound
Beam Technology |
|
TV
Hypnosis
Subliminal embeds in ads, TV, music, and video |
Micro-transmitters for FM, AM, TV, etc. |
Air Taser
Gun M-18 costs $350. The policeman's stun gun. Legal in many
areas.
Illegal in many areas. Restricted in some areas. |
|
| Top
Secret |
Computer sabotage of targeted computer(s).
URL Blocking.
Rare website viewing sabotage.
(Rain=100% chance for rally weather, for
example.)
Carnivore.
(link2)
1/14/05 FOIA info
Echelon.
(link2)
1. Probably
advanced Internet hacking tools and spyware.
2. Probably fancy hardware and software spy tools, including "rootkits".
3. Probably computer driver, software, and/or BIOS modifications.
4. Computer screen viewing tools.
4.1 ISP tools
that can
monitor all Internet activity.
4.2
TEMPEST
devices that can remotely view CRT (but maybe not LCD) computer
monitors by monitoring CRT EMF emissions.
4.3 Probably computer monitors that radio/transmit screen images
elsewhere. |
Probably
advanced electronic data gathering tools. Probably easier access
to private databases. |
Amazing but TRUE: Top secret
technology can sometimes read targeted minds.
Here is
some evidence (also
cached by Google) and
more evidence to document how this could technically be true.
Here is a
detailed scientific paper (in MS-Word format).
(It might be possible to combine an improved version of a
1976 Malech patent device for remotely reading brainwaves by
bouncing 2 mixed EMF beams off of a brain and reading filtered
bounced-back EMF data from the brain with other technology that can
translate brainwaves-to-speech. Also see
100
subliminal suggestion and mind-control patents.)
(It's probably brainwave reading, but it might also work using a
supersensitive mike that records internal "brain chatter".). |
Sound
Beam Technology,
FBI
Transponders,
Subliminal Sound Technology.
Probably improved acoustic
heterodyne/ hypersonic sound technology. |
Pulse-Beaming,
probably with Microwave Technology. (Very similar to rodent
repellant technology.) |
Brainwave Manipulation
(and monitoring and maybe even recording.)
Amazing technology feats
include: sound beam technology, subliminal messages, mind reading,
bodymind manipulation probably using brainwaves manipulation,
sleep now attacks, influencing dreams, and/or inflicting pain and/or
simulated illness. |
1.
Sound sabotage (and video soundtrack sabotage) technology.
ANY WORDS (or even
semi-subliminals) can be swapped in to song or video.
(Often combined with in sync
subliminal or semi-subliminal screwed up messages to the listener/
viewer.)
2. Remote-controlled machines can
be zapped with the correct (often infa-red) remote codes.
3. Computers and other devices can sometimes be partially controlled/
jammed using top-secret electronic zapping, |
Electronic warfare disorientation attacks and/or sleep attacks. |
Biowarfare
research labs. (Fort Dietrich, etc.) Also labs studying
highly infectious disease. |
| Whose at
Risk |
Everyone With a
Computer Connected to a Network and/or the Internet.
Employees at Work. |
Employees,
Customers,
Renters,
etc.
|
Employees at
Work.
"anybody with
Money, Power, Influence, or access to Sensitive, Classified, or
Personal Information..."
Subversives. |
Very Influential
(or powerful or rich) people receive more communication. |
People living in
crowded urban poverty.
Homeless.
Subversives.
Targeted individuals. |
TV viewers.
Information processors.
People with power, influence, and/or money.
Subversives.
|
Employees at Work using an employer's computer.
Kids with controlling parents.
Anyone connected to the Internet without quality firewall and
anti-virus programs. |
People who
threaten police armed with stun guns. |
An est.1 billion
people without clean drinking water.
Disease, spoiled food: Everyone's at Risk.
Poison: infants are at risk. |
| Self-Defense |
1. Computer access
password
2. Hardware Firewalls
3. Software Firewalls
4.
Anti-Virus software
5. Anti-Spyware software
6. Log off from the Internet when you're you not using it.
7. Hard Drive and
Data Backups
8.WiFi (wireless networks) passwords
9. Also anti-spam software. |
Unlisted phone
number (and/or street address).
P.O. Box. |
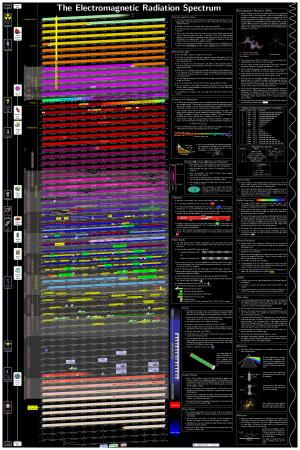
1.
Detailed
counter-surveillance ideas.
2. Read
real-world bugging
frequencies.
If bugs concern you, consider buying a bug detector and/or a frequency
scanner in order to maybe find any hidden bugs.
(Full scale spectrum analyzers are
probably way too expensive for you.)
(A cheap basic bug detector might
cost approx. $50 at ebay or $100 or more new and hopefully extend up
to 6 GHz. Excellent RF detectors cost more.)
3. Top secret locations might use expensive TEMPEST computers and/or
EMF shielded rooms. |
Anti-spam
software.
Soundproofing rooms for privacy. (Add more insulation between
rooms.) |
Nice private
home.
Nice neighborhood.
Microwave detectors/Bug detectors/RF detectors might be able to
document what is probably microwave pulsebeaming.
(Also, standard straight-line antennas
have the strongest signal when they point directly at the EMF
wave/beam source.) |
Carefully choose
quality TV.
Also at-risk people should be aware of capability of top-secret
mind-control technology in case they are ever hit with it. |
Computer security: a quality firewall and anti-virus scanner, etc.
Technology design suggestion: redesign wireless remotes so that they
can be wireless or wired with an optional cable attachment. |
Banning/regulating stun guns.
(On the other hand, stun guns might be used for non-lethal
self-defense.) |
Only drink good drinking water.
Basic food safety and personal hygiene.
Refrigerating food, freezing meat.
Also water purification plants for society.
|